Redefining Risk Ratings: Transforming Cybersecurity Metrics for Real-World Action
Risk ratings are a foundational element of nearly every cybersecurity strategy. They’re meant to help organizations prioritize vulnerabilities,...
Experiencing an active breach? Call us immediately at 1-866-405-9156 UncommonX has experienced ZERO reportable breaches.
3 min read
 Rich Pasewark - CEO, Board Director
:
Mar 20, 2026 12:39:52 PM
Rich Pasewark - CEO, Board Director
:
Mar 20, 2026 12:39:52 PM
We have been posting about the broad AI-powered capabilities in our platform for discovery and profiling and risk intelligence. These capabilities are designed to deliver on our "see everything and secure it" mission, providing the complete visibility necessary to properly understand your risk and secure an environment.
But visibility is only part of the equation. Once you can see everything, the next question is: what do you do about it? That is where AI Product Action Sets come in.
One of the most valuable, and at times underrated, capabilities of our system is the universal integration with over 300 networking, security, and cloud tools. These integrations provide value in processing logs, identifying alerts, and determining areas for optimization in the customer environment.
This matters because most security platforms are built to work within a single vendor ecosystem. If your environment includes a mix of products from different manufacturers, which nearly every environment does, traditional tools can only see part of the picture.
Our Exposure Management platform is brand agnostic. It works with what you have, regardless of who made it. And that is the foundation that makes AI Product Action Sets possible.
As we have expanded our AI capabilities to support more explicit instructions in our risk management and security operations, we are now offering an AI assistant to help IT and Security users understand how to configure and optimize their tools.
Network security often starts with switches and firewalls. These are critical infrastructure, and now with AI capabilities, we assess risk and provide instructions on how to improve security and resilience for particular product sets, often providing a more substantive viewpoint on how that system is situated in your environment.
To make this concrete, consider a Meraki switch in your environment. Our platform provides a deep dive on the switch, showing the traffic, the threats, and the sources. This is essential information for any network security team member.
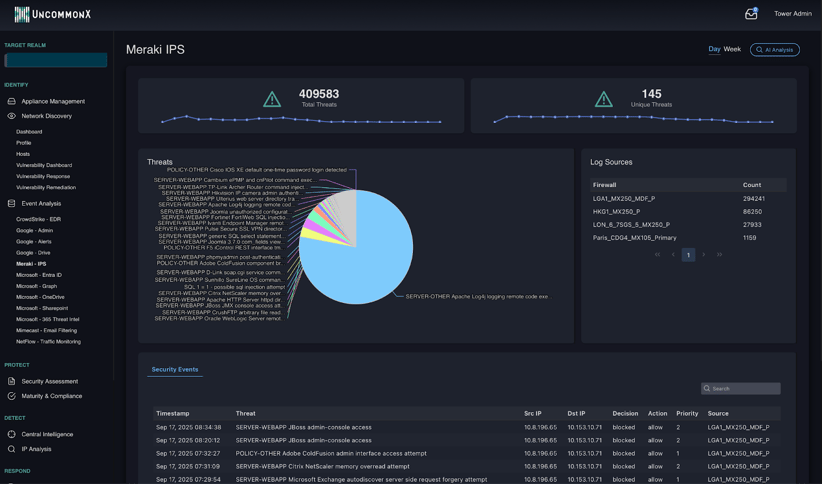
From there, our AI Analysis function reviews this data and provides explicit instructions to remediate and improve security and performance. Think of it as a magic button that interprets the product-specific risk and security data, uses our embedded AI models, and surfaces the recommended actions that will have the most positive impact on the environment.

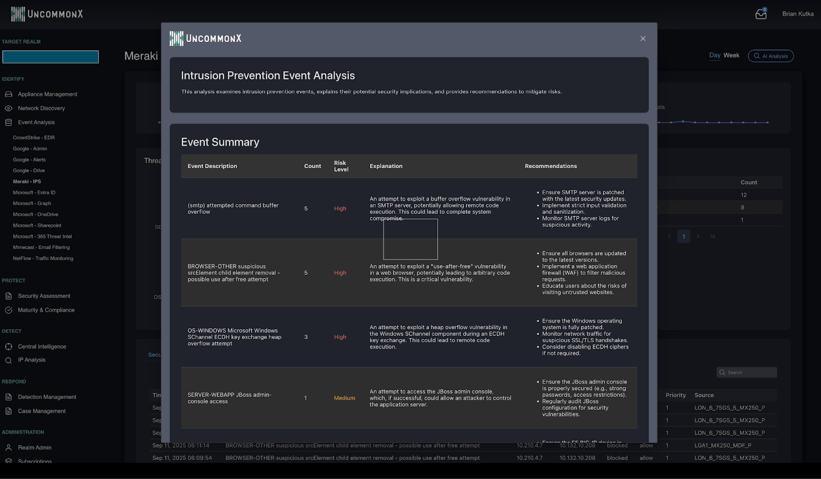
The result is not a generic list of suggestions. It is a prioritized, product-specific action plan tailored to how that device is actually operating in your network. Your team does not need to research best practices or consult vendor documentation. The instructions are ready to act on.
And this is not limited to switches. The same AI-driven analysis applies across your entire stack, from firewalls and endpoint protection to cloud configurations and identity management tools. Wherever there is an integration, there is an opportunity for our AI to surface specific, actionable improvements that your team can implement immediately. The more tools connected, the more comprehensive the intelligence becomes.
For CTOs, CIOs, CISOs, and security teams, AI-powered product actions make a meaningful difference in assessing risk and taking effective action, while utilizing resources in a cost-effective manner.
Most organizations only use 40 to 60 percent of their current tools' capabilities. Misconfigurations, unused features, and overlapping products are common. AI Product Action Sets help close that gap by showing you exactly how to optimize the investments you have already made, before you consider buying anything new.
Instead of spending hours investigating a risk and determining the right fix, your team receives explicit, product-specific instructions. That means less time researching and more time remediating. For teams that are already stretched thin, that efficiency matters.
Our goal is to provide a risk-centric action set that enables our clients to best leverage their existing investments. When you can see exactly what each tool is doing, where the gaps are, and how to improve configuration, you make better decisions about where to invest next. This is the power of AI applied to your data and needs.
In summary, our system applies AI to customer-specific data to evaluate parameters, probabilities, and potentials, generating explicit instructions that help teams reduce risk and improve performance across their entire technology stack.
Our next post will provide a deep dive into one of the most important areas of our AI capabilities: detections. Using our patented analytics and risk intelligence, our detections are faster and more powerful than almost any other system, and home in on real threats indicated by behavior, context, and vulnerability, not just alerts farmed from rote criteria.
Contact us today to learn how AI-powered product intelligence and our Exposure Management platform can help your organization get more from the tools you already own.

Risk ratings are a foundational element of nearly every cybersecurity strategy. They’re meant to help organizations prioritize vulnerabilities,...

Risk ratings are a staple in cybersecurity, but are they truly living up to their potential?

Exposure management is becoming a core discipline in cybersecurity, and for good reason. As environments grow more complex, fragmented tools and...