Strategies for Developing a Cyber Resilient School Culture
As the 2023/24 school year draws to a close, many districts are taking stock of the surge in cyber attacks that targeted educational institutions...
Experiencing an active breach? Call us immediately at 1-866-405-9156 UncommonX has experienced ZERO reportable breaches.
2 min read
Bilal Ibrahim, Senior Network Engineer
:
Mar 22, 2022 7:00:00 AM

Port security is a layer two traffic control feature on Cisco Catalyst switches. It enables administrators to configure individual switch ports to allow only a specified number of source MAC addresses ingressing the port. This helps improve security by filtering traffic that is destined to or received from a specific host based on their MAC address.
By default, there is no limit to the number of MAC addresses a switch can maintain on an interface and all MAC addresses are allowed. If you want, you can change this behavior with port security. For your organization’s internal network, you do not want an employee to bring their own switch and connect to the network. That could cause outages like a SPT topology change in a case where the new switch has a lower bridge ID or a VTP VLAN overwrites if the plugged switch has a higher revision number.
Port security can also help with:
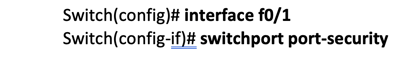
To avoid all the above harmful scenarios, we can use port security command. Configuring the port security feature is easy and there are no prerequisites for the configuration. Use switchport port security command to enable port security:
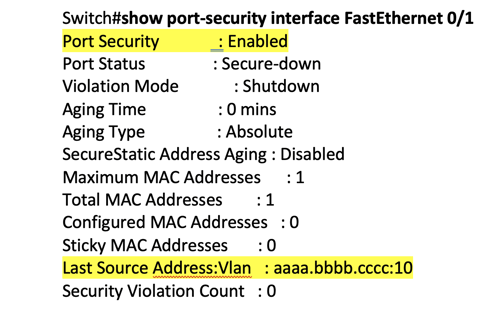
Below is a useful command to check port security configuration. You can tell that the security feature is enabled, and you can verify the source MAC address along with the VLAN (see highlighted lines).
There are multiple configurations that you can set using port security. First, you can set the maximum number of MAC addresses so that once the switch detects another MAC address on the interface, it will trigger the violation that was predefined by the administrator.
Second, you can filter the MAC address (hardcoding MAC address), and when the switch once again detects that this MAC address is not what has been configured, then it will trigger a violation action.
Below is an example of a violation penalty that was triggered because of a breach in port security settings:
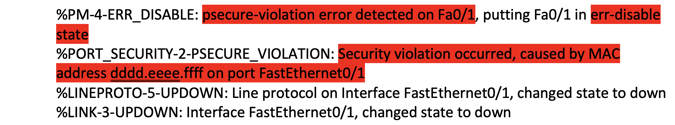
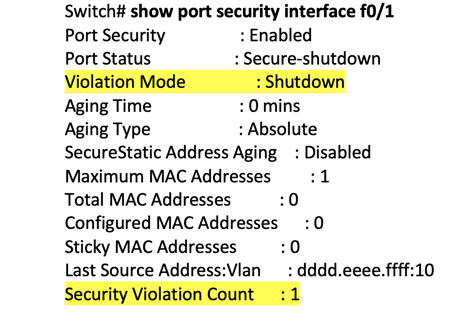
As we can see, the port goes into err-disable mode. We can use show port security interface command to get more details. Let’s take a close look at the output below:
You can enable the interface again after err-disable by either typing “shutdown”followed by “no shutdown” or even easier if the interface could recover automatically after a certain time (by default, 300 seconds) by using errdisable recovery cause pscure-violation.
You can decrease the waiting time and make it much faster. For example, instead of 300 seconds (about five minutes), we can set the time to 30 seconds using errdisable recovery interval 30.
Instead of manually typing the MAC address (hardcoding), you can make the switch automatically and use the first MAC address on the interface for the port security by adding the word Sticky at the end.
Instead of switchport port-security mac-address aaaa.bbbb.cccc, you can use switchport port-security mac-address sticky.
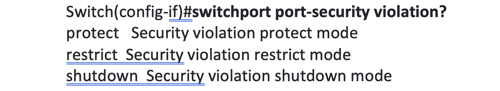
Here are violation predefined modes you can use:
For more about securing network access, contact UncommonX toda

As the 2023/24 school year draws to a close, many districts are taking stock of the surge in cyber attacks that targeted educational institutions...

The cybersecurity landscape in K-12 schools has reached a pivotal point. Despite growing threats, many schools find themselves underprepared, with a...
Google has released a security update addressing a zero-day vulnerability in the Chrome browser that is currently being actively exploited in the wild